- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
- cross-posted to:
- [email protected]
- [email protected]
- [email protected]
If this is indeed a security feature I’m about to buy my first iPhone.
CalyxOS and GrapheneOS have this as a feature.

Wouldn’t this make your phone reboot all night while you’re sleeping?
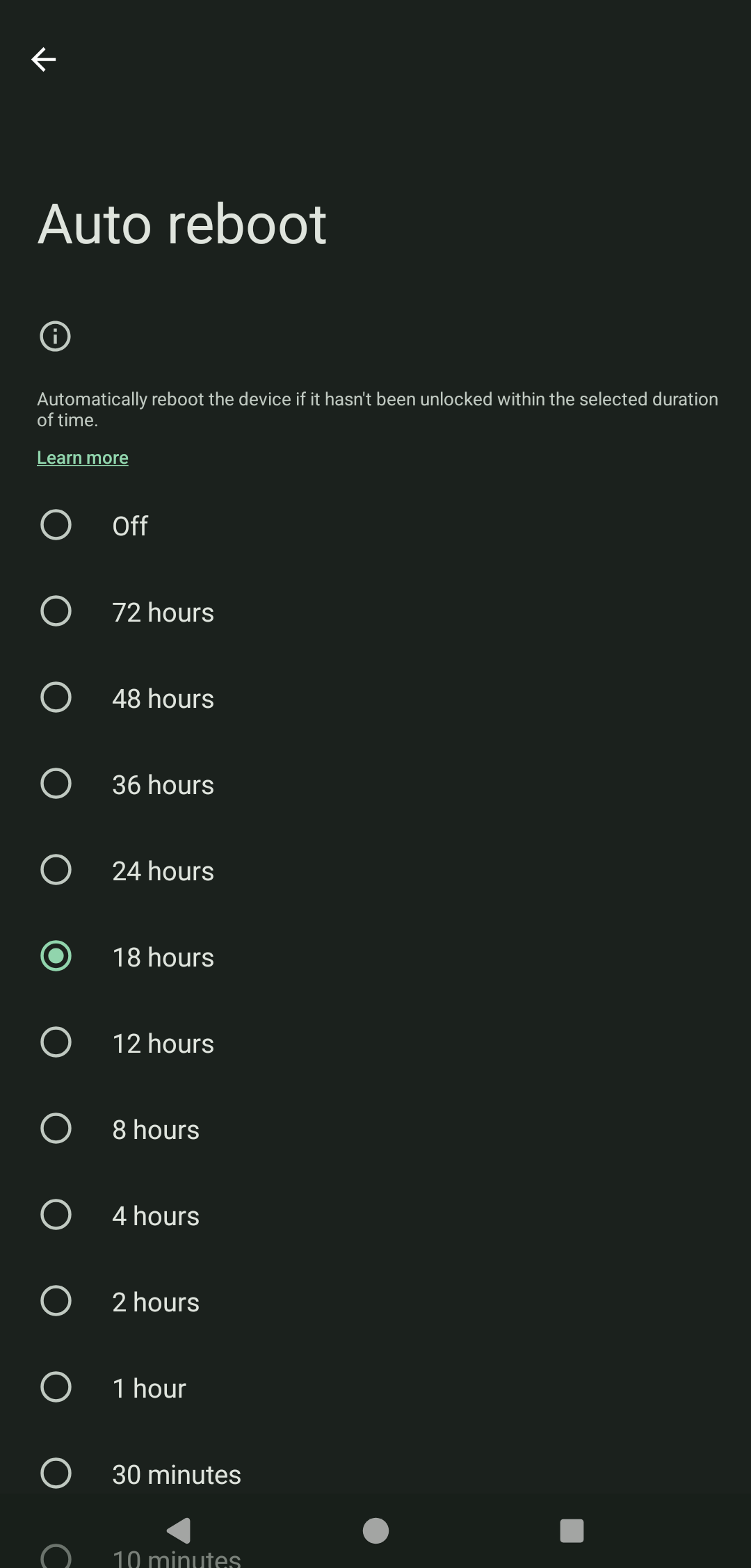
It will only reboot once unless it is unlocked again https://grapheneos.org/features#auto-reboot
Just set the time too longer than you would be asleep. So in this screenshot above you could set it to 18 hours and most people at least that I know do not go 18 hours without unlocking their phone at least one time which would then reset the timer.
Yes. Alternatively, you can just… power it off.
I keep mine on in case of family emergencies, it’s also my alarm clock
The only solution would be to simply turn the setting off at night, or have developers add an automatic scheduling option. Of course, you can just set the timer to be longer than your sleep schedule as well, but then you miss out on security.
Iirc phone calls and alarms still work after a reboot in the lock status, it just disables biometric unlock and keeps the filesystem encrypted
Well, funny thing–I was once late for a job because my alarm didn’t go off. Guess why? Yep, auto reboot. There was even a notification saying the alarm didn’t go off. Very odd behaviour, but that’s what happened.
Presumably it doesn’t reboot unless it was already unlocked.
You can adjust the time.
Two hours seems extremely low.
On grapheneos it’s a setting, 18 hours by default I believe, but adjustable from 10 minutes to 72 hours.
That seems much more reasonable. Thanks for the info.
What is the good thing about a phone rebooting?
When you input your password, then your biometrics (faceID, fingerprint, etc) become active. A restart requires you to enter that again. The police can make you put your finger on your phone or look at it, but they can’t make you divulge your password without a court order.
There are have also been some exploits that are possible ONLY while the machine is booted and already in that state unlocked state, rebooting relocks all the HW encryption and clears main memory.
Law enforcement have tools to bypass lockscreens and access the data on the device. They use backdoors and exploits, so older phones are more vulnerable. Most exploits only work if the phone has been unlocked at some point since it was booted.
This is why law enforcement keep them powered-on, and in a faraday cage. They are in a state with a better chance of unlock, but have no signal so nobody can remotely find/lock/wipe it.
Don’t switch to a privacy-violating platform just for a feature found in open source operating systems.
Oh yeah, see they’ve done it perfectly by having it based on the last time you unlocked your screen.
This makes me even more interested in getting a newer pixel with graphene on it. I had the Pixel 3a back in the day, but have been using other devices since then with lineage. But this right here may very well bring me back. The only thing they need to do is have it on by default and set it to like a long time frame like 24 or 36 hours.
On GrapheneOS, it is on by default and set to 18 hours. It makes sense to me to have the default be less than 24 hours.
I agree. I was thinking of 18 hours myself because 12 seems a little bit too short. But 24 or above seems far too long.
You can change it to what you need, i think default is 18
Back in the day? I’m reading this on a Pixel 3a.
I had a screen issue with mine after a while where the bottom right hand corner of the screen was trying to separate from the body a little bit and there was like this green line that showed up in the middle of my display. It was annoying as hell. Also, that was before I started only letting my battery charge up to 80% and so my battery was pretty well shot by the time that occurred as well.
Android has it as well. It’s customizable, too.
It should be, but it appears to be a bug.
Which is really sad quite frankly and if they did add it as a feature it should have a cooldown period of like 48 hours where it reboots twice in that time frame just so that if a cop turned the setting off it would still not help them
apple is not in business to obstruct law enforcement
You say obstruct, I say protect users from totalitarian regimes
apple’s entire existence depends on the US government… whose team do you think they play for?
so 3 Trillion USD apple is trailing a FOSS project on issues of security. checks out lol
Bug has been promoted to feature
SWEET!
It is a feature on grapheneos :)
Just use a pattern to lock your phone. Police can’t do shit if you have that set up.
It’s not the lock, it’s the fact that phones are usually encrypted after a reboot (to oversimplify). As the article says you have extra security measures to protect a freshly booted phone.
Android has an app that you can install that auto wipes a phone after X amount of time if the phone hasnt been unlocked:
https://f-droid.org/en/packages/me.lucky.wasted/
Also theres an app that allows you to set a fake password that wipes the phone:
https://f-droid.org/en/packages/me.lucky.duress/
All open source, I have tested these apps on my phones, they work great. The second app about the duress password is a bit glitchy and didnt work on some of my phones.
Disclaimer: I am not a lawyer and setting your phone to automatically wipe itself may be considered destruction of evidence in a court of law.
Nice, I think making your phone go into Before First Unlock mode cannot be considered destruction of evidence
Well they might charge you with “Obstruction of Justice” instead. Then plug it in some cellebrite device and boom, unlocked.
Best way to not have to deal with stuff like this is just to not have the incriminating evidence in the first place. If you are, for example, doing a protest, only chat with contacts in a safe place, then wipe chat logs every time, any data you wish to keep should be encrypted then uploaded anonymously via VPN/Tor and wiped from local storage. Hide the fact that such data exists so you wouldn’t have a scenario where the government is trying to get you to give them the data, since they dont even know what data exists. Plausable deniability.
Edit: Those apps I’ve linked is still a good idea since “Destruction of Evidence” is probably a lesser charge than something like “Rioting”.
Cellebrite struggles with iPhones already, this reboot is part of the cat and mouse game they’re playing
That’s what they say. I mean the news literally base this off the FBI’s own words, so there’s no way for us to tell if they actually manage to break the encryption but then turns around that say “the encryption is too strong”. Besides, iOS is closed source.
Intelligence agencies have made this “Anom Phone” that is this supposed encrypted phone that drug dealers and various criminals used to communicate, turned out to be a honeypot.
I’ve used cellebrite before.
Anecdote of 1 for you, iOS is a pain in the ass.
There are different versions.
One is where they sell the cellebrite device to law enforcement.
Another where the cellebrite device remain in control of cellebrite, and law enforcement has to send the phone to cellebrite.
Unless you actually work for cellebrite and got access to their more advanced tools, which then I doubt they would let you share the details of since that must be breaking some non-disclosure agreement.
Yes, I am well aware.
shipping a phone to them or waiting for the tech to arrive, that transit time, is what my mind went to immediately when this feature was introduced.
The phones are significantly more difficult to get into after the reboot.
I’m disclosing absolutely nothing.
Cellebrite? I don’t think that’s how encryption works
It might work that way, actually .
Just because the phone is encrypted doesn’t mean there’s not an exploit that makes it easier to bypass or extract the passphrase. Celebrite is unfortunately pretty good at attacking out of support phone and breaking into them.
Use a modern, supported OS on a device put out by a trusted vendor and you’re probably ok. But old software/hardware makes it much easier to bypass.
Apparently some phones have a totally isolated electrically separated microcomputer which is in charge of encryption and decryption. Your phone doesn’t actually know how the encryption decryption is done because it’s separated from the microcontroller.
Any attempts to modify the microcontroller or replace any of its components with more cooperative components, will result in all of the data being wiped. This is implemented at the firmware level with the instructions being in ROM.
There are attacks where rather than trying to crank the password you just capture the hash which is stored in memory somewhere and then using a tool that lets you bypass the standard login inject that hash into the app, totally bypassing the UI interface and the password hashing algorithm.
The app sees the hash is correct and isn’t aware that the information has been input via nonstandard methods, and so allows access.
The attacker still doesn’t have a clue what your password was, but they don’t need to. Interestingly enough this means that every time they want access to your data they have to do this because they don’t have a way of actually changing the password or finding out what it was.
Link? That sounds incredibly stupid design
Yeah. It is. Every design has assumptions and every design can be abused by those assumptions. I’d like to say it’s not a failure in design but it’s really just a failure of imagination. No one thought this would be an issue, turns out it is, so someone fixed it.
The problem is that not every system gets updated.
Thanks but I literally cannot figure out how to use these apps after installing
For the “Wasted” app:
-
Check the box saying “Wipe Data” (you can optionally check wipe eSim if yiu also want that to happen)
-
Tap the bottom button saying [Off] which would ask you to give permission to the app as a Device Administrator, giving it the power to wipe your device.
-
Tap the gear button on top right
-
Scroll down to the “Lock” and check that
-
Tap the upper left button with the 3 horizontal lines
-
Tap the “Lock” menu option
-
Enter a value. I personally would use something like 24 or 48 hours. Note that 24H automatically becomes 1D in the app, idk why but thats just some weird quirks with the app.
For the Duress app, it doesn’t really work anymore on the phone I’m using, so you might have to do your own testing.
Edit: Make sure you dont get drunk and passed out for 24 hours because then your phone gets wiped lol. Good luck, I didn’t make the app so be careful with it, don’t blame me if your accidentally get your device wiped when you didnt want it to.
Edit 2: Also you cant really know if these apps works on your particular phone unless you test it yourself, that means wiping it. So you might wanna back up your phone then trigger the wipe to see if it works. Dont wanna get caught at a protest only to find out the app failed.
-
Anything to make their job harder is perfectly okay by me. The only thing that would be needed would be for this to be a feature and to have a cool down period of like 48 hours where the phone would reboot twice in that time so that if it was held it would still reboot itself.
Edit: Even better idea. Turning off the feature requires a reboot.
Note to those wishing for such a function, it’s possible by creating an iOS Shortcut - New Shortcut > Shutdown > Change it to ‘Restart’.
From there, you create an automation in Shortcuts to run based on time, location, etc.
Alas, it asks if you want to restart.
You could always take 10 seconds and invoke the operating system’s hard shutdown command if you have the 10 seconds to spare. On Android at least, that’s pressing and holding power and volume up for 10 seconds. But I do not know what it would be on the iPhone.
It would be best if the function was like if the phone has not been unlocked for at least 16 hours then reboot automatically. A time thing would be a problem though because then it would just reboot every day and that would be no fun.
I saw elsewhere this is a new feature in iOS 18.1, so it will probably pretty solid I’d think. But for shortcut wise, at minimum I suppose one could put automations that trigger when it detected within certain geofences or something… but then whenever you drive by your local police station it will kindly reboot your phone every time lol
What if they thought you would do that and specifically took it to a police station that you did not have a geofence for? Mind you, they wouldn’t necessarily know. But it’s not impossible.
It also might not be taken to a police station. Who knows where the actual forensics labs are. No real need for them to be on-site or even labeled.
If you have the 10 seconds, you could use the operating system’s hard reboot function, which at least on Android is pressing and holding power and volume up for 10 seconds. But I don’t know what it is on the iPhone.
Power and volume up for new phones, and then power and home for older ones with Touch ID.
Also, so you know, if you press power 5 times it will ask if you want an emergency call, say no, but after you do it your PIN is required to unlock. No biometrics work at that point. So, no one can force you to touch or look at it. I don’t know if it puts the phone in that “mode” or not, but it’s a handy trick.
Yeah, I knew that that was available, but I do not know whether it puts the phone in the before first use mode, like you mentioned, or just disables the biometrics, but leaves the device in after first use mode.
this is the police we’re talking about, they probably just forgot to charge them and are trying to shift the blame
Whatever it is, incompetence, bug, or feature, I love it.
Hot take: this is actually a bug not a feature.
Which is the saddest part, honestly. If it was a feature, that would be fantastic news. And especially if it had a cooldown feature of like 48 hours, where it would reboot twice in that timeframe, so that if a cop turned off the setting, while it was in their possession, it wouldn’t matter because it would reboot anyway.
Someone said it in another thread yesterday, baseband memory leak. The firmware for that shit is terrible, I’ve had to deal with it in the past.
Apparently, there’s at least a chance that it is an intentional feature instead of a bug. There’s a comment link below somewhere in this thread that mentions it.
That seems at odds with release notes someone else found.
“new security feature” “warning”
🙂
I guess if you have the 10 seconds to do so, you could invoke the operating system hard reboot function, which at least on Android is pressing and holding power and volume up for 10 seconds. I don’t know what it is on the iPhone.
Edit: Too bad there’s not some sort of haptic to let you know that it accepted the command before it shuts down though.
Long press of power and volume up for a few seconds puts you into BFU.
Does it or does it just simply disable biometrics but leave it an AFU? I would hope that if it’s going to disable the biometrics, that it would put it in BFU. But I do not know.
I don’t know how it works under the hood, but from a user perspective it behaves like it’s in BFU. Biometrics disabled, phone code required.
Yeah, don’t get me wrong. Disabling the biometrics and requiring the pin is a good step. But I would like to see somebody test it to figure out whether it actually goes into BFU mode or not.
Speculation is that ios 18 is communicating with other phones while locked to determine security. This can more likely be a NSA/US empire backdoor than a user protection feature. Lowly police systems are just not on the “hacker list”. One way the backdoor could work is that if a “NSA/Mossad list phone” is present, protect the other phones, unless the phones are in an NSA/Mossad secure facility.
Or it could just be using the inactivity reboot feature that was recently added to iOS.
ok. I’d suspect spy agency back doors if the feature was unannounced. If it was an announced feature, then that is reasonable explanation.
It’s literally a documented feature AND it’s weird super secret spy agency shit is the easiest answer for you tbh.
I thanked you for explanation. OP did not suggest that as an explanation.
You did though. Lmao
The police could just ask Apple, it isn’t like they are going to have some secret reboot process that they would hide from the police.
And what would Apple be able to do about it? They don’t have your password*, so they’ll be just as unable to decrypt the device as the police.
*you can give them your password via iCloud I believe but you don’t have to
I’m not saying apple will do anything about it, just that they will let the cops know what is causing the reboots if asked.
Phones that are repeatedly attempted to be unlocked auto hard reset. Been a feature for years.
This is not for devices where the pin has been entered incorrectly too many times. This is for devices that the police have seized and are awaiting forensics to pull data from.