This is really good for encrypted content such as a hard drive, password vault or gpg key
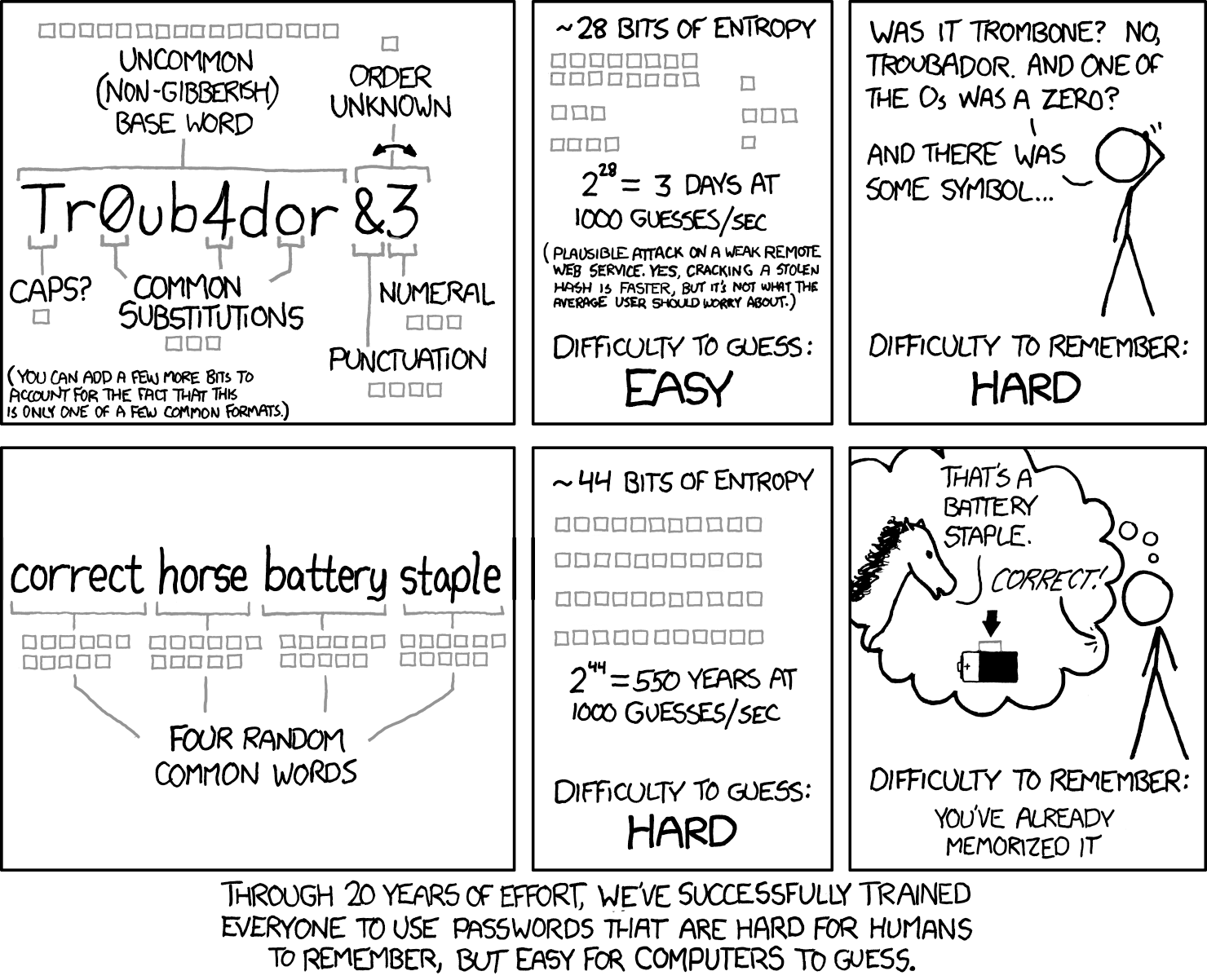
So TL;DR, the XKCD method, but with six words instead of four and using a larger wordlist?
If you haven’t got any dice handy you can use random.org to generate the numbers for you. Or even select a set of words from the list
Shameless self-plug: if you want something without Cloudflare in front of it dicewa.re is nice. Keep in mind though that in general it is not recommended to rely on random number generators as their source of randomness cannot be verified.
Doesn’t using a particular wordlist limits choice, gives attackers a wordlist to generate the password from
Technically, yes. But the article already mentioned the amount of effort for the brute force to succeed (that is, practically never, if the phrase is truly random.)
But anyway. With regular passwords, the attackers already have a list: the alphabet plus numbers and symbols. Not really that different.
It is a good technique to be sure, but I haven’t found it useful in my everyday life. In practice 99% of my passwords are stored in my password manager. I only remember like 3 passwords myself. For those I want them to be easy to type as I do it semi-regularly (whenever I turn on my computer or phone, my phone sometimes re-verifies, …). These may be slightly easier to remember but end up being much longer. I find that I don’t have issues remembering the 3 passwords that I actually regularly type.
In fact I recently switched my computer passwords to be all lowercase, just to make it easier to type. I’ve offset this reduced entropy by making them longer (basically shift+key is similar entropy to key+key and easier to type, especially on phones or on-screen keyboards).
The recommended 6 words produces incredibly strong passwords. The equivalent with all lowercase would be 16.5 characters. Personally I went for 14 characters and in my threat model that is very very secure. But this will also depend on your attack model. If it is a disk encryption password or other case where you expect that the attacker can get the hash then it will depend on the strength of the hash and possible attacker’s computing power. If it is protected by a HSM that you trust you can get away with short PINs because they have strict rate limits. Any decent online service should also have login rate limits reducing required entropy (unless the leak the hash without resetting passwords, then see the above point where the attacker gets the hash). All of my memorized passwords fall into the category of needing very strong security but I still found that remembering a random character password that only only took about a week when entering it once a day.
I also think encryption password security depends heavily on the hash. A hash that’s takes along time to break will be more secure and will require a shorter password to be secure
Yeah, that is what I meant by “strength of the hash”. Probably should have been more clear. Basically the amount of resources it takes to calculate the hash will have to be spent by the attacker for each guess they make. So if it takes 1s and 100MiB of RAM to decrypt your disk it will take the attacker roughly 1s and 100MiB of RAM for each guess. (Of course CPUs will get faster and RAM will get cheaper, but you can make conservative estimates for how long you need your password to be secure.)
Parallelism 1, iterations 15, memory 512mb
New status unlocked! LUNATIC
Nobody remembers diceware?
Eff has a better list imo. Diceware has a tonne of short abbreviations like “1st”. Eff is words that are mostly 5 to 8 characters long. Much more xkcd like and easier to make a mnemonic out of.






